If you’re trying to understand the difference between AES and RSA, you’re likely looking for clear, practical guidance on which encryption method fits your specific use case. Whether you’re securing sensitive data, building an application, or evaluating cybersecurity protocols, knowing how these two standards compare is critical to making the right decision.
This article delivers a direct, technically grounded aes vs rsa comparison, breaking down how each algorithm works, where they’re typically used, and why they’re often implemented together rather than chosen as strict alternatives. We focus on real-world performance, security strengths, key management differences, and scalability considerations—so you can move beyond surface-level definitions.
Our insights are based on established cryptographic standards, current security best practices, and practical implementation knowledge used across modern systems. By the end, you’ll have a clear understanding of when to use AES, when to use RSA, and how to apply both effectively in secure environments.
Choosing Your Digital Shield
In any aes vs rsa comparison, the real difference is mathematical design. AES (Advanced Encryption Standard) is symmetric, meaning one shared key encrypts and decrypts data. RSA (Rivest–Shamir–Adleman) is asymmetric, using public and private keys.
Why it matters:
- AES is up to 10–100x faster in bulk data tests (NIST benchmarks).
- RSA key sizes must be 2048 bits or higher for modern security (NIST, 2023).
Real-world proof? HTTPS uses RSA to exchange keys, then switches to AES for session traffic. Use AES for data at rest; use RSA for secure key exchange in transit data.
Understanding AES: The Symmetric Workhorse for Bulk Data Encryption
At its core, symmetric encryption uses a single secret key to both encrypt and decrypt data. Think of it like a shared house key—whoever holds it can lock or unlock the door. The most trusted example is Advanced Encryption Standard (AES), a block cipher that processes data in fixed 128-bit blocks through repeated rounds of substitution (swapping bytes) and permutation (shuffling them). This layered scrambling is what makes brute-force attacks computationally impractical.
AES isn’t just popular—it’s proven. The U.S. National Institute of Standards and Technology (NIST) selected AES in 2001 after rigorous public testing, and it remains approved for classified government data. Today, it secures everything from Wi-Fi (WPA3) to cloud storage.
Why AES dominates bulk encryption:
- Exceptional speed and low CPU overhead
- Efficient for encrypting large datasets (data at rest)
- Hardware acceleration support in modern processors
In any aes vs rsa comparison, AES consistently outperforms RSA in speed, making it ideal for encrypting entire databases rather than just small keys.
AES-128, AES-192, and AES-256 differ by key length. While AES-128 is still considered secure, AES-256 offers exponentially greater resistance to brute-force attacks and is approved for top-secret information. (Yes, that’s military-grade for a reason.)
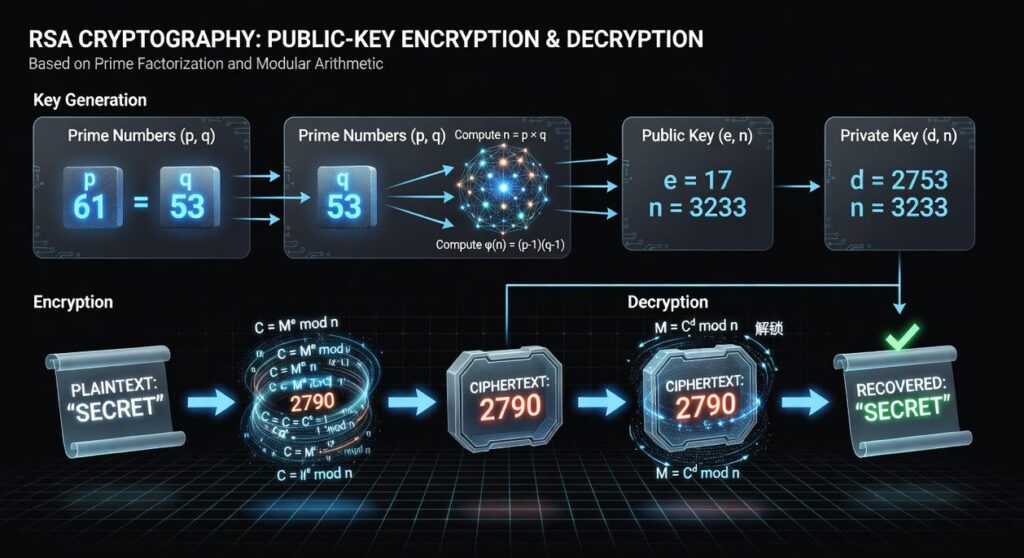
Understanding RSA: The Asymmetric Pioneer for Secure Key Exchange

Asymmetric encryption (also called public-key cryptography) is a system where two mathematically linked keys do different jobs: a public key encrypts data, and a private key decrypts it. RSA, introduced in 1977 by Rivest, Shamir, and Adleman, is the most recognized implementation of this model (ACM, 1978).
Think of RSA like a public mailbox. Anyone can drop a letter in using the public slot, but only the mailbox owner with the private key can open it. Behind the scenes, RSA relies on the practical difficulty of factoring the product of two massive prime numbers—a task that would take classical computers an impractical amount of time (NIST).
Key Features and Benefits
| Feature | Technical Detail | Benefit |
|---|---|---|
| Key Pair System | Public + Private keys |
Solves the key distribution problem |
| Digital Signatures | Private key signs data | Verifies authenticity and integrity |
| Security Basis | Large prime factorization | Strong mathematical protection |
Critics point out that RSA is slower than symmetric methods like AES—and they’re right. In any aes vs rsa comparison, RSA consumes more computational power. However, its ability to securely exchange keys and enable trusted digital signatures makes it indispensable for HTTPS, email encryption, and secure software updates.
Head-to-Head Comparison: Performance, Security, and Use Cases
When comparing AES (Advanced Encryption Standard) and RSA (Rivest–Shamir–Adleman), the differences become clear almost immediately. Have you ever wondered why your device can encrypt an entire hard drive in seconds but struggles with certain secure handshakes? The answer lies in computational overhead—the processing power required to perform encryption.
Speed and Efficiency
First, let’s talk performance. AES is a symmetric encryption algorithm, meaning it uses the same key for encryption and decryption. Because of this design, it’s incredibly fast and efficient. In fact, AES is orders of magnitude faster than RSA and is commonly used for encrypting files, databases, and even full disk systems like BitLocker (NIST FIPS 197).
RSA, on the other hand, is asymmetric. It relies on a pair of keys—public and private—and complex mathematical operations. As a result, it’s significantly slower. Would you encrypt a 10GB file with RSA alone? Probably not—unless you enjoy watching progress bars move at a glacial pace.
Key Management and Distribution
However, speed isn’t everything. AES requires both parties to securely share the same secret key. That’s easier said than done. How do you transmit that key without exposing it?
This is where RSA shines. You can distribute a public key openly while keeping the private key secret. Anyone can encrypt data with the public key, but only the private key holder can decrypt it. That’s RSA’s core advantage—and the foundation of secure protocols like TLS. If you’re curious about how that works in practice, see what is tls 1 3 and why it improves online security.
Primary Function and Security Strength
So what’s the real aes vs rsa comparison takeaway? AES handles the actual data encryption (confidentiality), while RSA secures the AES key during exchange (authenticity and key transport).
In terms of strength, a 2048-bit RSA key offers security roughly comparable to a 128-bit AES key (ECRYPT II). That contrast highlights AES’s efficiency: far smaller keys, similar protection. Efficient, right?
Practical Application: How AES and RSA Work Together in the Real World
In the real world, encryption is a team sport. TLS/SSL (the protocol behind HTTPS) blends RSA and AES into a hybrid system that’s both secure and fast.
Here’s how it works:
- RSA securely exchanges a secret session key.
- That shared key is then used with a faster AES algorithm.
- AES encrypts all data in the session.
In my view, any aes vs rsa comparison misses the point—they’re partners, not rivals. RSA locks the door; AES guards the house. It’s like handing over a secret handshake before starting a private conversation.
The verdict is simpler than the endless aes vs rsa comparison debates suggest. You’re not choosing a winner; you’re solving a coordination problem.
The frustration? Teams either OVERCOMPLICATE the stack or ignore performance until everything slows to a crawl. We’ve all seen it.
Here’s the balance:
- Use RSA to securely exchange keys and create digital signatures.
- Use AES to encrypt bulk data at high speed.
Think of it like a buddy-cop movie: one negotiates, one handles the heavy lifting.
Architect a hybrid system. Generate a session key, protect it with RSA, then encrypt data with AES. Problem solved.
Mastering Encryption Choices for Stronger Digital Security
You came here to clearly understand how modern encryption methods protect your data and which approach makes the most sense for your needs. Now, you have a practical grasp of the strengths, trade-offs, and real-world applications behind symmetric and asymmetric encryption — especially through a clear aes vs rsa comparison.
Choosing the wrong encryption method can slow performance, expose vulnerabilities, or create unnecessary complexity. In today’s rapidly evolving tech landscape, that risk is too costly to ignore. The right encryption strategy isn’t just a technical decision — it’s a competitive advantage.
If you’re serious about securing sensitive data, optimizing performance, and staying ahead of emerging cyber threats, now is the time to act. Explore proven encryption strategies, implement best-practice security frameworks, and follow trusted insights that break down complex cryptography into practical action steps. Don’t leave your data exposed — strengthen your encryption strategy today.
 Johnny Websteringser writes the kind of tech innovation alerts content that people actually send to each other. Not because it's flashy or controversial, but because it's the sort of thing where you read it and immediately think of three people who need to see it. Johnny has a talent for identifying the questions that a lot of people have but haven't quite figured out how to articulate yet — and then answering them properly.
They covers a lot of ground: Tech Innovation Alerts, Buzzworthy Data Encryption Protocols, Gadget Trends and Emerging Tools, and plenty of adjacent territory that doesn't always get treated with the same seriousness. The consistency across all of it is a certain kind of respect for the reader. Johnny doesn't assume people are stupid, and they doesn't assume they know everything either. They writes for someone who is genuinely trying to figure something out — because that's usually who's actually reading. That assumption shapes everything from how they structures an explanation to how much background they includes before getting to the point.
Beyond the practical stuff, there's something in Johnny's writing that reflects a real investment in the subject — not performed enthusiasm, but the kind of sustained interest that produces insight over time. They has been paying attention to tech innovation alerts long enough that they notices things a more casual observer would miss. That depth shows up in the work in ways that are hard to fake.
Johnny Websteringser writes the kind of tech innovation alerts content that people actually send to each other. Not because it's flashy or controversial, but because it's the sort of thing where you read it and immediately think of three people who need to see it. Johnny has a talent for identifying the questions that a lot of people have but haven't quite figured out how to articulate yet — and then answering them properly.
They covers a lot of ground: Tech Innovation Alerts, Buzzworthy Data Encryption Protocols, Gadget Trends and Emerging Tools, and plenty of adjacent territory that doesn't always get treated with the same seriousness. The consistency across all of it is a certain kind of respect for the reader. Johnny doesn't assume people are stupid, and they doesn't assume they know everything either. They writes for someone who is genuinely trying to figure something out — because that's usually who's actually reading. That assumption shapes everything from how they structures an explanation to how much background they includes before getting to the point.
Beyond the practical stuff, there's something in Johnny's writing that reflects a real investment in the subject — not performed enthusiasm, but the kind of sustained interest that produces insight over time. They has been paying attention to tech innovation alerts long enough that they notices things a more casual observer would miss. That depth shows up in the work in ways that are hard to fake.