If you’re searching for a clear, actionable way to protect your devices, data, and digital privacy, this secure home network guide is built for you. With cyber threats growing more sophisticated each year, a basic router setup is no longer enough to keep your personal information safe. You need practical steps, smart configuration tips, and up-to-date security practices that actually work in real-world home environments.
In this article, we break down exactly how to strengthen your network—from optimizing router settings and implementing strong encryption protocols to segmenting devices and improving overall performance. The goal is simple: help you build a home network that’s fast, resilient, and secure.
Our guidance is grounded in current cybersecurity standards, hands-on testing of consumer networking hardware, and analysis of evolving threat patterns. By the end, you’ll have a clear, step-by-step understanding of how to reduce vulnerabilities and take full control of your home network security.
Fortify Your Digital Castle: A Practical Home Network Security Guide
Your home Wi-Fi network is the digital front door to your bank accounts, smart cameras, and late-night messages. Yet most routers still run DEFAULT passwords and outdated encryption—an open invitation to attackers.
In this secure home network guide, you’ll disable WPS, switch to WPA3 (the latest Wi-Fi encryption standard), segment IoT devices, and enable DNS-level filtering. Competitors often stop at “change your password.” We go further: firmware audits, MAC address monitoring, and bandwidth anomaly alerts that flag intrusions early.
Think of it as installing deadbolts, cameras, and a moat (yes).
Securing the Core: Your Wi-Fi Router’s Essential Settings
Your router is the front door of your digital home. Yet many people leave it protected by the factory username and password like “admin/admin.” These default credentials are publicly documented, which means hackers can guess them in seconds. Log into your router’s web interface by typing its IP address into your browser, open the Administration or System tab, and create a long, unique password. (Pro tip: use a password manager.)
Next, update the router’s firmware—the built-in software that controls how it works. Manufacturers release firmware updates to patch security vulnerabilities, similar to phone updates. Visit the Firmware or Advanced settings section and click “Check for Updates.” Skipping this step is like ignoring a broken lock.
For Wi-Fi protection, enable WPA3 encryption. Encryption scrambles data so outsiders cannot read it. WPA2 was strong, but WPA3 adds individualized data encryption and better defenses against password guessing attacks, according to the Wi-Fi Alliance. In Wireless Settings, choose WPA3-Personal as your security mode.
Finally, disable WPS (Wi-Fi Protected Setup). WPS lets devices connect using a PIN or push button, but researchers have shown its PIN system can be brute-forced. Turn it off in Wireless or Security settings.
These steps form the backbone of any secure home network guide, transforming your router from easy target to hardened gateway. Regular checkups every few months ensure new threats are blocked before they spread, keeping smart TVs, laptops, and game consoles safely connected at all times. Without cutting corners.
Creating Digital Boundaries: Guest Networks and Firewalls
Why a Guest Network Is NON-NEGOTIABLE
Your main Wi-Fi holds laptops, work files, banking apps, and cloud backups. A guest network is a separate access lane that isolates untrusted devices like visitors’ phones or smart lightbulbs from that sensitive data. Think of it as a digital waiting room: they get internet, not your network’s inner workings. Some argue it’s overkill for small homes, but even one compromised gadget can expose everything else.
How to Set It Up
- Log into your router by typing its IP address into a browser.
- Find “Guest Network” in Wireless or Advanced settings.
- Enable it, create a NEW, STRONG password, and disable access to local devices.
Pro tip: use a passphrase over 16 characters.
Activate Your Firewall
Most routers include an SPI (Stateful Packet Inspection) firewall. It acts like a traffic cop, tracking outgoing requests and blocking unsolicited incoming connections. Confirm it’s enabled under Security settings. If you’re following a secure home network guide, this step should be mandatory. Together, guest networks and firewalls create layered defense that actually works.
Small steps now prevent massive headaches later. Protect your data before problems start.
Advanced Protection: Filtering Malicious Content with DNS

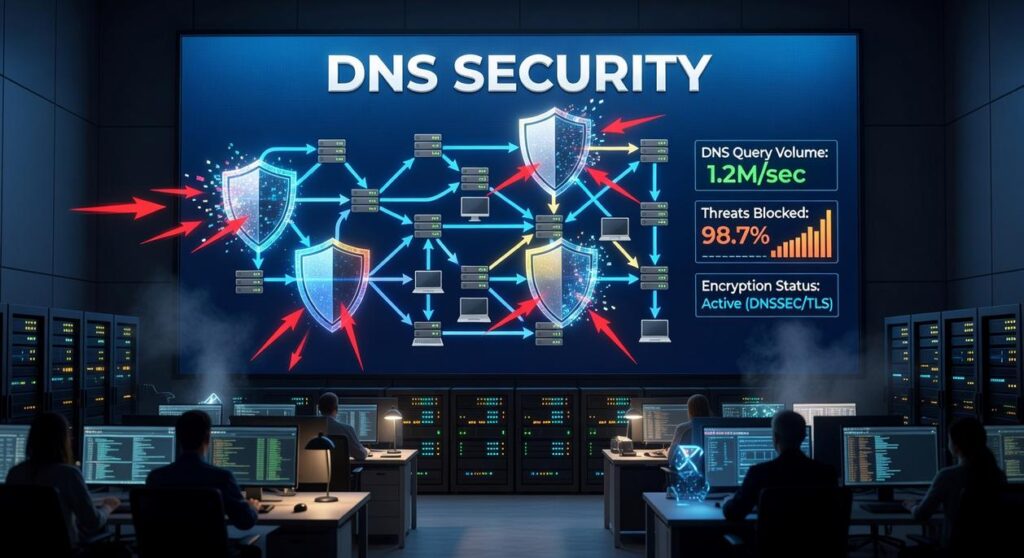
What Is DNS Filtering?
The Domain Name System (DNS) is often called the internet’s “phonebook.” It translates human-friendly domain names into IP addresses computers understand. DNS filtering takes that a step further: it blocks requests to known malicious domains before your device even connects.
Instead of relying solely on antivirus software (which reacts after a threat lands), DNS filtering PREVENTS the connection in the first place. According to the FBI’s Internet Crime Report (2023), phishing caused over $3.4 billion in losses in a single year. Many of those attacks relied on fake domains. Block the domain, block the scam.
Think of it as a bouncer for your Wi-Fi (no name on the list, no entry).
Choosing a Secure DNS Provider
Two trusted, FREE options stand out:
- Cloudflare (1.1.1.1 for Families) – Offers malware blocking and optional adult content filtering. Cloudflare reports sub-20ms global query speeds, making it one of the fastest public resolvers.
- Quad9 (9.9.9.9) – Automatically blocks domains flagged by threat intelligence from IBM X-Force and other security partners.
Some argue ISP-provided DNS is “good enough.” But ISPs often lack advanced threat feeds and may log browsing data. Independent providers focus specifically on security and privacy.
PRO TIP: Choose a provider that publishes transparent threat intelligence sources.
How to Change DNS Settings on Your Router
Log into your router’s admin panel (typically 192.168.1.1), find DNS settings under WAN or Internet configuration, and replace the default addresses with:
- 1.1.1.1 and 1.0.0.1, or
- 9.9.9.9 and 149.112.112.112
Save and reboot.
This ensures EVERY device on your network inherits protection automatically. For deeper optimization, review our guide on best practices for reducing cloud infrastructure costs and pair it with a secure home network guide for layered defense.
The Final Layer: Smart Device and User Habits
Lock down every IoT device you own. Cameras, speakers, thermostats, even smart plugs ship with default passwords that hackers can guess in seconds (yes, really). Change them immediately and update firmware regularly. Good password hygiene means:
- Using a password manager to generate long, unique logins
- Enabling two-factor authentication on banking, email, and exchange accounts
For step-by-step basics, review a secure home network guide and apply it device by device. Finally, stay vigilant: phishing emails and shady links bypass tech defenses if you click first and think later. Stay alert always.
Your Blueprint for Ongoing Digital Safety
You’ve already taken steps: fortified your router, isolated smart devices on a guest network, and enabled content filtering. That’s not basic protection—that’s a layered defense strategy.
Here’s why it matters. In cybersecurity, layered security means multiple safeguards working together so one failure doesn’t expose everything (think castle walls, moat, and guards).
To keep momentum:
- Check for router firmware updates every quarter.
- Review connected devices and remove unknown entries.
- Revisit your filtering settings after adding new gadgets.
Security isn’t a one-time task. Revisit secure home network guide and adapt as threats evolve.
Lock Down Your Network with Confidence
You came here looking for clear, practical steps to protect your digital life—and now you have them. From understanding encryption protocols to optimizing your router settings and eliminating hidden vulnerabilities, you’re no longer guessing about your network’s safety.
The real risk was never just slow speeds or dropped connections. It was exposed data, weak passwords, outdated firmware, and silent entry points hackers exploit every day. Ignoring those gaps can cost you privacy, money, and peace of mind.
Now it’s time to act. Revisit this secure home network guide, apply each step methodically, and run a full security audit on your setup today. Don’t wait for a breach to discover what you missed.
If you want deeper protection strategies, advanced optimization tips, and trusted insights relied on by thousands of security-conscious readers, explore our expert resources now. Take control of your network security today and turn your weakest link into your strongest defense.