If you’re searching for a clear, practical understanding of decentralized network fundamentals, you’re likely trying to cut through the hype and grasp how these systems actually work. With blockchain platforms, peer-to-peer applications, and distributed protocols reshaping the digital landscape, it’s essential to understand the core principles that make decentralized networks secure, resilient, and scalable.
This article breaks down the essential components behind decentralized architectures, from consensus mechanisms and node distribution to encryption standards and fault tolerance. Rather than offering surface-level definitions, we focus on how these elements interact in real-world environments and why they matter for performance, privacy, and long-term sustainability.
Our insights are grounded in ongoing analysis of emerging technologies, protocol upgrades, and security research, ensuring you get accurate, up-to-date explanations. By the end, you’ll have a solid foundation to evaluate decentralized systems with confidence and make informed technical or strategic decisions.
Beyond the Buzzword: What Truly Makes a Network Decentralized?
Decentralization gets tossed around like a Silicon Valley catchphrase, but it has teeth. A network is decentralized when control, validation, and data storage are distributed across independent participants rather than a single authority. Think Bitcoin’s node operators versus a bank database.
To evaluate claims, focus on decentralized network fundamentals: consensus mechanisms, node diversity, governance structure, and permissionless access. If one company can pause the system, it is not decentralized (no matter the whitepaper).
My recommendation: audit codebase, check validator concentration, and prioritize systems with transparent governance. Choose substance over marketing gloss.
The Foundational Triad: Distribution, Immutability, and Transparency
At the heart of blockchain systems lies a powerful trio. These decentralized network fundamentals work together to create security, resilience, and trust—without relying on a central authority (yes, even without a “guy behind the curtain” pulling levers).
1. Distributed Architecture
First, distribution means the ledger exists across thousands of independent nodes. Instead of one central server, copies live everywhere. As a result, there’s no single point of failure. If one node goes offline—or gets attacked—the network keeps running. Critics argue centralized databases are faster and cheaper to maintain. Fair point. However, resilience matters: according to IBM, distributed systems significantly reduce downtime risks compared to centralized infrastructures. In practical terms, that means stronger censorship resistance and greater uptime for global users.
2. Cryptographic Immutability
Next comes cryptographic hashing. Each block contains a hash (a fixed-length digital fingerprint) of the previous block. Change one record, and the fingerprint changes—breaking the chain. Altering past data would require redoing massive computational work across most nodes, which is computationally infeasible in large networks (as outlined in the original Bitcoin whitepaper). Some skeptics worry about errors being permanent. True—but immutability protects against fraud far more often than it locks in mistakes.
3. Unwavering Transparency
Finally, public ledgers allow anyone to verify transactions. Transparency builds trust without intermediaries. While privacy advocates raise concerns, many networks use pseudonymous addresses to balance openness and discretion.
Practical Optimization: Compared to centralized databases, this triad boosts data integrity, uptime, and tamper resistance. Pro tip: always evaluate how many active nodes secure a network before trusting its durability.
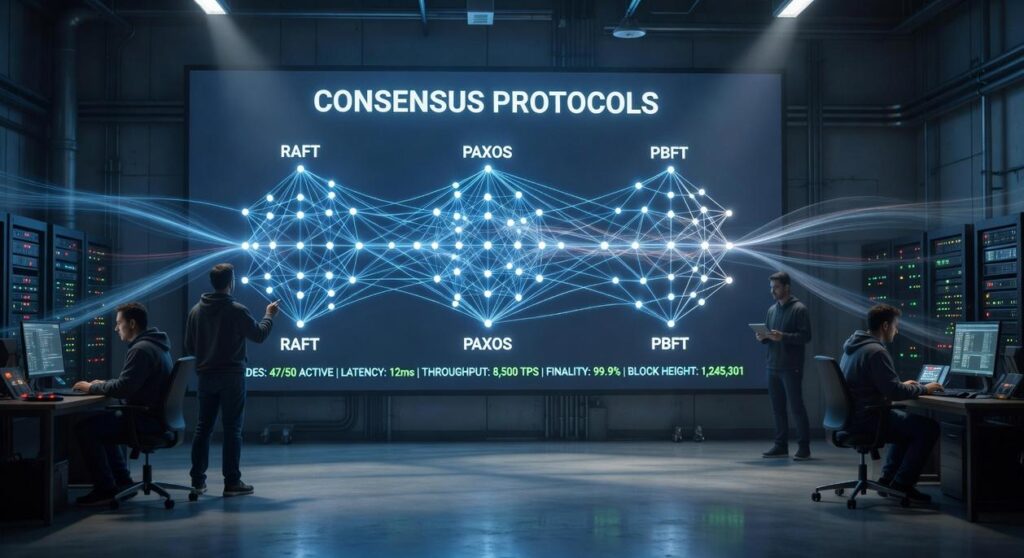
Consensus Mechanisms: The Engine of Trustless Agreement
What Is Consensus?
At its core, a consensus mechanism is the protocol that allows participants in a blockchain network to agree on the state of a shared ledger—without relying on a central authority. Instead of a bank or clearinghouse verifying transactions, the network collectively validates them using cryptographic rules. This process is foundational to decentralized network fundamentals, ensuring transparency, immutability (meaning records can’t easily be altered), and security.
In simple terms, consensus is how strangers on the internet agree on “what’s true.” (And unlike group chats, there’s math involved.)
Proof-of-Work (PoW)
First introduced by Bitcoin in 2009, Proof-of-Work (PoW) requires miners to solve complex mathematical puzzles to validate transactions and add new blocks. The first to solve the puzzle earns the right to append the block—and collect a reward.
Strengths:
- Extremely secure due to computational difficulty
- Highly decentralized when mining is widely distributed
Weaknesses:
- Energy-intensive (Bitcoin’s annual consumption rivals that of some small countries, per Cambridge Bitcoin Electricity Consumption Index)
- Slower transaction throughput
Critics argue PoW is environmentally unsustainable. That’s a fair concern. However, supporters counter that much mining now uses renewable energy and that security at this scale requires significant resource investment.
Proof-of-Stake (PoS)
In contrast, Proof-of-Stake (PoS) selects validators based on how much cryptocurrency they “stake” (lock up as collateral). The more you stake, the higher your chance of validating transactions.
| Feature | Proof-of-Work | Proof-of-Stake |
|——————-|————–|—————|
| Energy Use | High | Low |
| Security Model | Computation | Economic stake|
| Scalability | Limited | Improved |
PoS drastically reduces energy use and improves scalability. Ethereum’s transition to PoS in 2022 reduced energy consumption by over 99% (Ethereum Foundation).
However, skeptics point out a risk of wealth concentration—those with more tokens gain more influence. Still, mechanisms like slashing (penalties for bad behavior) help maintain accountability.
Beyond the Big Two
Innovation continues. Delegated Proof-of-Stake (DPoS) allows token holders to vote for validators, improving efficiency. Meanwhile, Proof-of-History (PoH), used by Solana, timestamps transactions to enhance speed.
Ultimately, consensus design shapes a blockchain’s performance, security, and decentralization. And as new models evolve, the debate isn’t about which is perfect—it’s about which trade-offs best serve the network’s goals. For deeper cryptographic context, explore what is homomorphic encryption and why it matters.
Data Encryption Protocols: Securing a Decentralized World
The Role of Public-Key Cryptography
At the heart of modern blockchain systems is public-key cryptography—a method that uses a key pair: a public key (shared openly) and a private key (kept secret). Think of your public key like an email address and your private key like the password that proves it’s really you. When you authorize a transaction, your private key creates a digital signature that verifies ownership without exposing sensitive data.
What’s in it for you? Sovereign control. No bank approvals. No centralized gatekeepers. Just you and your keys. According to NIST, properly implemented public-key systems make unauthorized access computationally infeasible (NIST SP 800-57). That’s not just security—it’s autonomy.
Critics argue key management is risky (lose the private key, lose access). True. But hardware wallets and multi-signature setups dramatically reduce that risk. Pro tip: always back up private keys offline in multiple secure locations.
Hashing in Action
A hashing algorithm converts data into a fixed-size string of characters—its digital fingerprint. Even a tiny change in input creates a completely different hash. This ensures integrity without revealing the original information.
It’s like sealing a letter with wax. If the seal’s broken, you know it’s been tampered with. SHA-256, used in Bitcoin, exemplifies decentralized network fundamentals by securing blocks against alteration (FIPS 180-4).
Practical Security Benefits
These protocols prevent double-spending, secure peer-to-peer communication, and enable pseudonymous participation. You transact confidently, verify instantly, and protect your identity—without sacrificing transparency.
For deeper technical context, explore resources like this cryptography overview.
In a world where data breaches dominate headlines, encryption isn’t optional—it’s empowerment.
Building on bedrock, the pillars of distribution, immutability, consensus, and encryption work together as the interlocking engine of decentralization. Distribution spreads power; immutability locks records; consensus aligns strangers; encryption protects truth. Skeptics argue these are just technical upgrades, but they represent a structural shift toward open, equitable, resilient systems. Think beyond code: this is civic infrastructure for the internet. If you want to prepare, focus on understanding decentralized network fundamentals and how they power DeFi, NFTs, and DAOs. • Study protocols. • Test wallets and governance tools. Ask yourself: what could you build on such bedrock? Choose participation over passivity.
Mastering What Comes Next in Crypto Innovation
You came here to better understand how emerging technologies, encryption protocols, and decentralized network fundamentals shape the future of crypto and digital systems. Now you have a clearer picture of how these pieces connect — and why ignoring them can leave you vulnerable, outdated, or missing major opportunities.
The real challenge isn’t access to information. It’s knowing how to apply it before the market shifts again. Weak optimization, poor security practices, and shallow technical knowledge are exactly what hold projects and investors back.
If you’re serious about staying competitive, start implementing stronger encryption standards, optimize your systems for performance, and deepen your understanding of decentralized architectures today — not later.
Don’t let outdated strategies slow you down. Get expert-driven insights, actionable optimization techniques, and cutting-edge crypto analysis trusted by thousands of forward-thinking readers. Subscribe now and stay ahead of the curve before the next wave hits.